Since some months now, we maintain specific Yara rules to detect phishing kit sources (.zip files). Phishing kits sources are sometimes left on the host serving phishing pages.
Using the StalkPhish project (see https://stalkphish.com/products/stalkphish/) we used to collect phishing kits in order to extract e-mails addresses, Telegram channels (see https://stalkphish.com/2020/12/14/how-phishing-kits-use-telegram/), and so on.
In order to sort our zip files collection we use our phishing kit Yara rules (see https://stalkphish.com/products/phishingkit-yara-rules/).
About these Yara rules
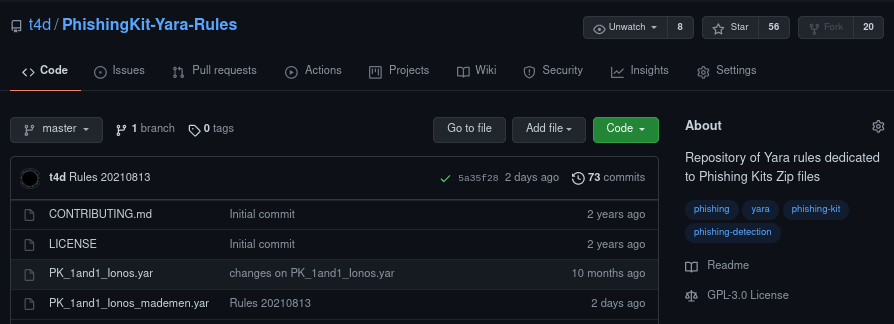
Today the repository count 211 Yara rules for several threats and brands, all these rules are free of use and are published under the GNU GPLv3 licence.
You can find these rules on GitHub: https://github.com/t4d/PhishingKit-Yara-Rules
For rule analysis we use the VirusTotal YARA-CI plugin on the GitHub repository, this permit to control if rules are correct and don’t contain mistakes before being used.
These rules are created using phishing kit sources we grab every day and are named with the brand name and a actor/team name we can obtain from the sources:
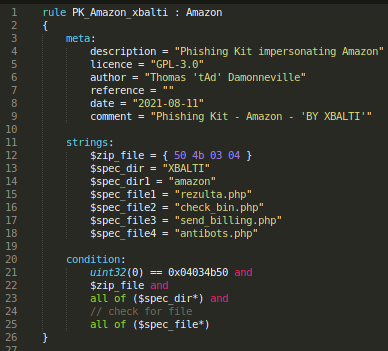
These rules go to parse the Zip file to find specific names of files and directories, in the example above, all specified files and directories must exist for the file to be considered as matching the Yara rule.
Of course you can participate to the project, creating your own Yara rule and making a pull request on the repository. Please try to respect the contribution rules, you can find here: https://github.com/t4d/PhishingKit-Yara-Rules/blob/master/CONTRIBUTING.md
Using phishing kit Yara rules
Using official yara binary (apt install yara, for example), you can use each phishing kit Yara rule on your file/directory, like this:
$ yara PK_impots_gouv_fr_azubi.yar /data/dl
PK_impots_gouv_fr_azubi /data/dl/http__pqok.justns.ru_information.zip
PK_impots_gouv_fr_azubi /data/dl/https__adorid.com_hih_Impots20.zip
PK_impots_gouv_fr_azubi /data/dl/http__hosting2078368.online.pro_Impots.zip
[...]
You can create a unique .yar file with all phishing kit Yara rules inside and use it in the same command. By default Yara can’t use a directory containing .yar files as an argument.
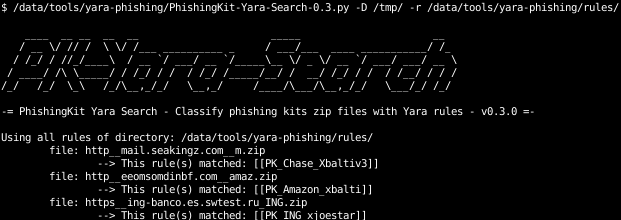
Also you can use the python tool we called PhishingKit-Yara-Search made to use a directory containing all the rules as a argument: https://github.com/t4d/PhishingKit-Yara-Search
You can use it to scan 1 file with all yourYara rules:
$ /data/tools/yara-phishing/PhishingKit-Yara-Search-0.3.py -f /tmp/http__eeomsomdinbf.com__amaz.zip -r /data/tools/yara-phishing/rules/

Or use all your Yara rules to fully scan a directory:
$ /data/tools/yara-phishing/PhishingKit-Yara-Search-0.3.py -D /tmp/ -r /data/tools/yara-phishing/rules/
VirusTotal
Since some months now these Yara rules from our project are implemented in VirusTotal‘s analysis. Dropping a file to VT for analysis will, if a PhishingKit Yara rule exists, give you this information as crowdsourced YARA Rules into the detection section (you have to be logged in to see this part):

You can check the matching rule for further details:

Keep in touch
For all our news about these rules our other projects you can follow us on Twitter or our blog! As we told you above: don’t hesitate to particpate to this open source project, you know, to make Internet a safer place 🙂

Discover more from StalkPhish - phishing, scam and brand impersonation detection
Subscribe to get the latest posts sent to your email.