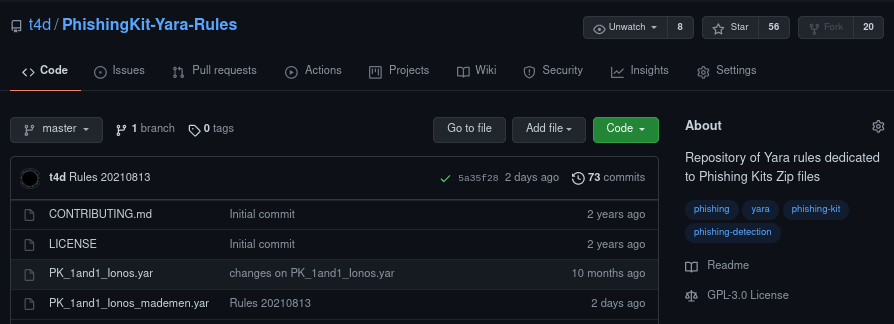
As a reminder, the PhishingKit-Yara-Rules project is a free and open source project which provides several dozen phishing kit detection rules contained in zip archives. You can find these rules on GitHub: https://github.com/t4d/PhishingKit-Yara-Rules
We have already covered the creation and use of Phishing Kit Yara rules in a previous post (see: https://stalkphish.com/2021/08/17/using-phishing-kit-yara-rules-project-for-phishing-kits-detection-and-triage/).
Specifically, these are rules intended for the detection and sorting of archives of phishing kits.
We covered how to use the PhishingKit-Yara-Search project to use these rules, as well as VirusTotal’s use of these rules.
But do you know you can use these rules with ClamAV too?
Using PhishingKit-Yara-Rules with ClamAV
As many threat analysts, we often embed the free antivirus engine ClamAV in our analysis stacks. First, because it’s always good to check files you are manipulating during a threat analysis, and because this antivirus is free (big thanks to the dev community!).
Since the 0.99b (yes… it was 2015) you can use Yara rules to scan files in a directory, using the clamscan binary with -d argument, you force to use Yara rules as database.
First, you need to clone the rules repository:
$ git clone https://github.com/t4d/PhishingKit-Yara-Rules
Then you ‘just’ have to declare the directory of your Yara rules following the -d argument, then follow the directory you have to scan:
$ clamscan -d /data/tools/yara-phishing/rules/ /tmp/Stalkphish_phishing-kits/
The clamscan binary do what it have to do, and you just have to catch the report for the result:

Yes, two lines of code, no more 🙂
Some last words, you can join the StalkPhish community on Keybase: https://keybase.io/team/stalkphish or our page on LinkedIn: https://www.linkedin.com/company/stalkphish
Enjoy!
Discover more from StalkPhish - phishing, scam and brand impersonation detection
Subscribe to get the latest posts sent to your email.