During our regular analysis of our data, collected mainly by our Stalkphish.io service, we came across a phishing kit targeting Coinbase and its customers.
Coinbase is a ‘place to buy and sell cryptocurrency’. These kinds of platforms used to store, buy and sell cryptocurrencies are increasingly targeted by scammers, just like traditional banks.

The particularity of this kit is that it adds a part of interactivity between the victim and the scammer: the scammer can interact with the victim in real time to get information that can be used only in a limited time, this is the case of MFA data.
About MFA
It is now known among users that the only login and password used as a connection factor are no longer secure enough to secure access to a portal or data, which is why it is now more than recommended to use multifactor authentication methods (MFA).
Multi-factor authentication allows you to add additional data (such as texts, biometrics, FIDO2 security keys and one-time passcodes) to log in.
This technology prevents an attacker, a scammer, who might have stolen your login/password pair from being able to log in to your account, since this second authentication factor (we also call it 2FA) is single-use: even if it is stolen it cannot be re-used.
The phishing kit – hosting and development
This phishing kit was downloaded on December 27, 2022 by one of Stalkphish.io’s sensor. One of the purposes of Stalkphish is to retrieve phishing kits sources to extract interesting information about the actors of the campaign: chasing bullet-proof servers will not contribute significantly to the fight against phishing, trying to stop the actor is the only way to fight efficiently against phishing.
Retrieving phishing kit sources permit to analyze the kit, in order to improve our knowledge of the techniques used by scammers.
Stop the actor is the only way to fight efficiently against phishing.
The phishing kit was deployed on the IP address 34.83.148.63, an IP address belonging to Google Cloud. The domain name chosen by the scammer was booked 2 days before, on December 25th, it is cbase-userhelp[.]com, the choice of ‘cbase‘ corresponds to the usurped brand: Coinbase.
Several kits were deployed between December 27 and 28 on this same domain name according to Stalkphish.io, 2 Coinbase kits as well as an Affirm kit. All these phishing kits are produced by the same developer: HadySpeed. However, this does not mean that this is the scammer operating the campaign, as the scammer may have purchased the kits as well as the smishing tool that HadySpeed sells:
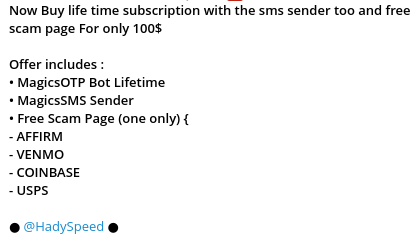
We won’t go any further in this study about this kit developer, but don’t hesitate to ask us if you want to know more.
The phishing kit – configuration files
Once downloaded and unzipped, this is what the ZIP archive looks like:
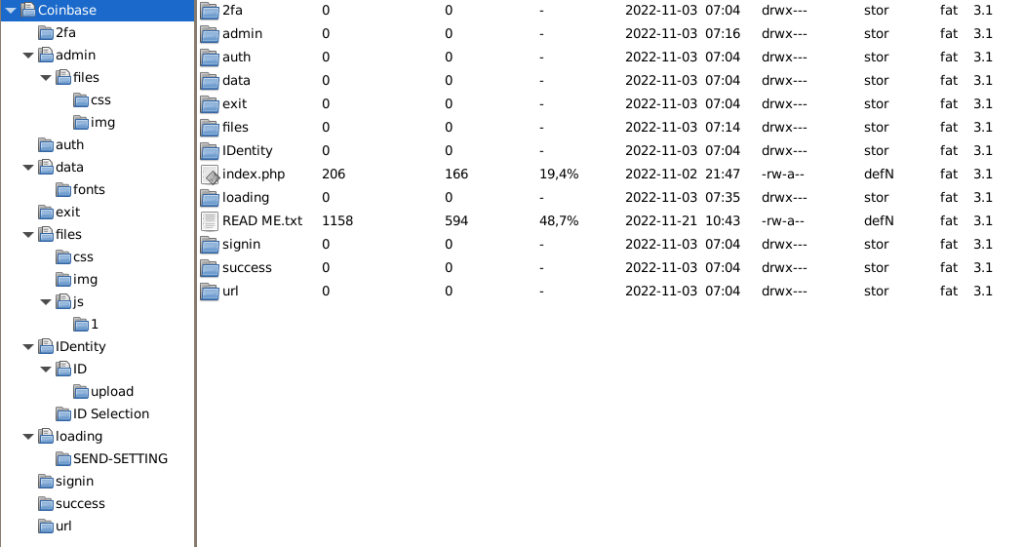
First over all we open the READ ME.txt file :
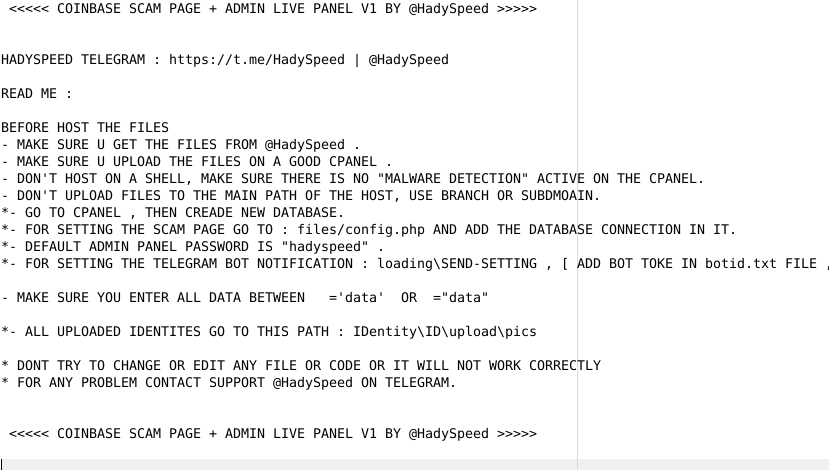
This file contains important information about :
- the author and version of the kit
- how to install the kit, on a cPanel in particular
- the configuration of the database
- the name of the global configuration file (files/config.php)
- the default password of the admin panel
- the files containing Telegram bot configuration
- the directory that will receive the ID card pictures (IDentity\ID\upload\pics)
This how looks the configuration file (files/config.php):
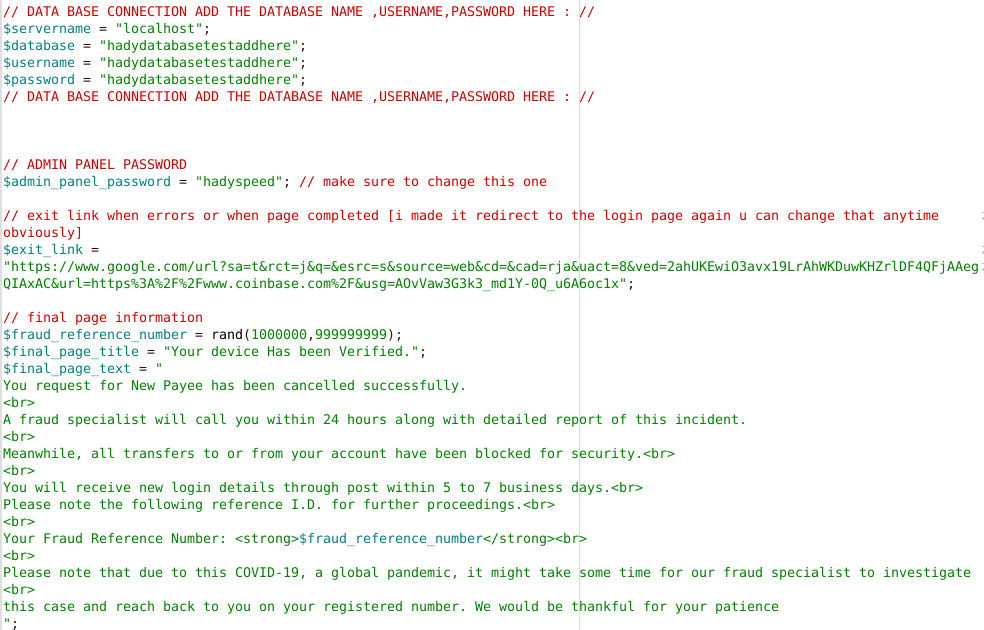
The following information can be obtained from the configuration file:
- the name of the database and its credentials
- the password of the administration page of the kit
- the link to where the user is redirected and the message displayed when the user has finished filling in the requested information
This information allows us to learn more about the kit:
- it uses a database to store the stolen information
- an administration panel is available
- …
The phishing kit – pages
This phishing kit is divided into different pages and phases with the aim of stealing several types of data related to a Coinbase account:
- login and password to connect to the Coinbase account ;
- scan of a driver’s licence ;
- second authentication factor delivered by SMS or another OTP app
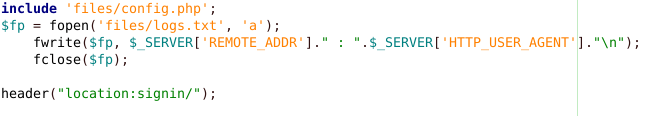
Looking at the first index.php file – the first page you launch when you connect to the phishing page – we can see that the connections are logged (IP address and user-agent) in a text file at the root of the kit.
We can also notice the absence of access filters, where usually a multitude of files dedicated to stop the connections of phishing page detection bots.
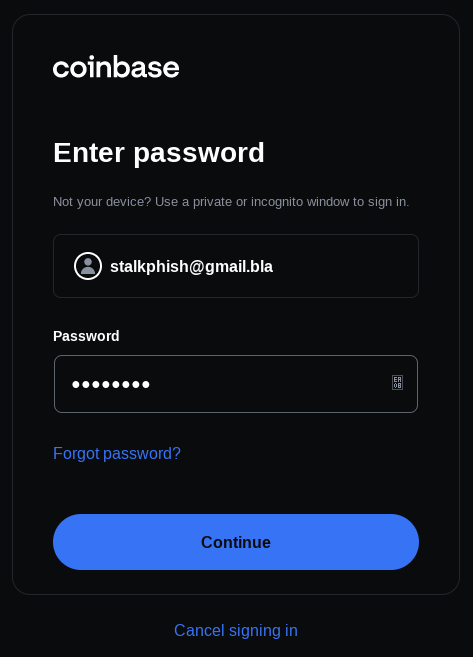
So we access the first page which presents the Coinbase login screen, the signin/index.php file:
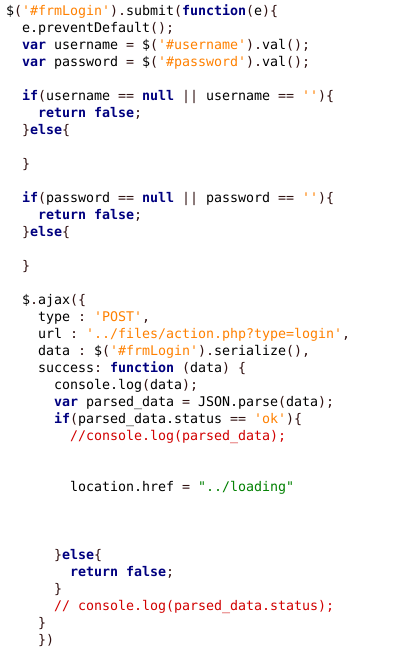
Once the login data is entered, the page makes an AJAX call to the files/action.php page and assigns a unique identifier to the victim’s browser session ($uniqueid)…
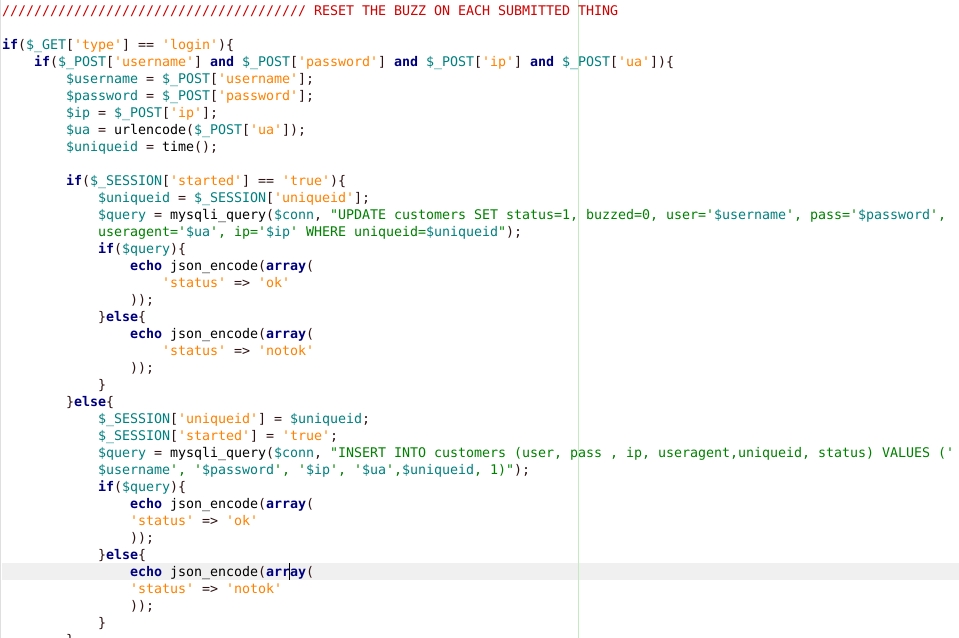
… then the data (login, password, user-agent, IP address, uniqueid) are entered in the MySQL database. By the way, observe the comment appearing in the file/action.php page and which concerns the ‘buzz‘, we will come back to it:
The victim’s browser is then routed to the loading directory, which contains an index.php file, this file will perform some few checks, especially if the uniqueid is not present (then back to the first page).
This page is in charge of sending a hit through Telegram, indicating to the scammer that a user has just connected and sending him the uniqueid of the victim.
Once the alert is given, indicating that a victim has presented himself on the phishing page and has started to enter his information, the scammer will be able to go to the administration panel to interact with the victim:
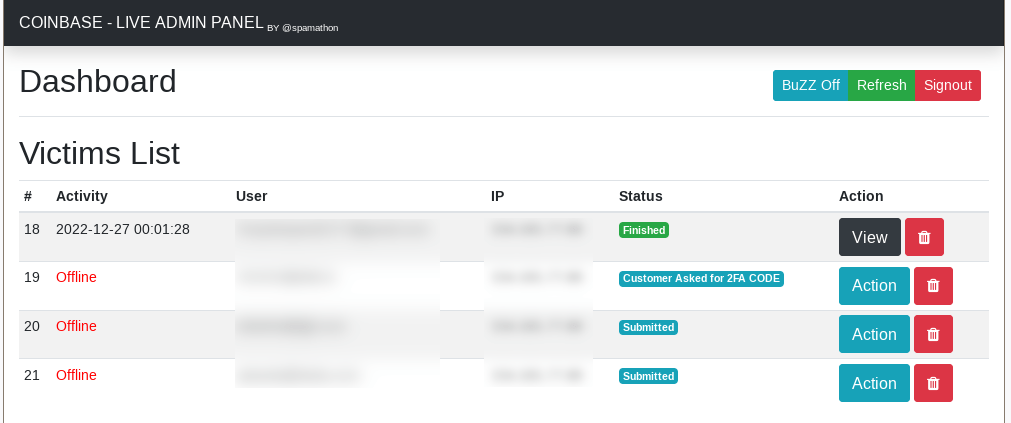
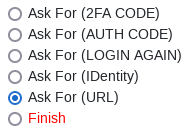
From now on, the scammer can communicate in real time, not through direct communication with the victim, but through the pages presented on the phishing site. The kit allows to push several types of pages depending on the data that the attacker wants to recover, here are the options that are proposed from the administration page:
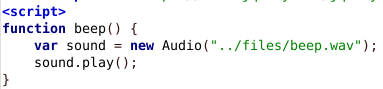
Then, at each action of the victim, the buzzer (we talked about it above), will be triggered to warn the scammer that the action is continuing:
As we have seen before, a page asking for the driver’s license upload can be requested:

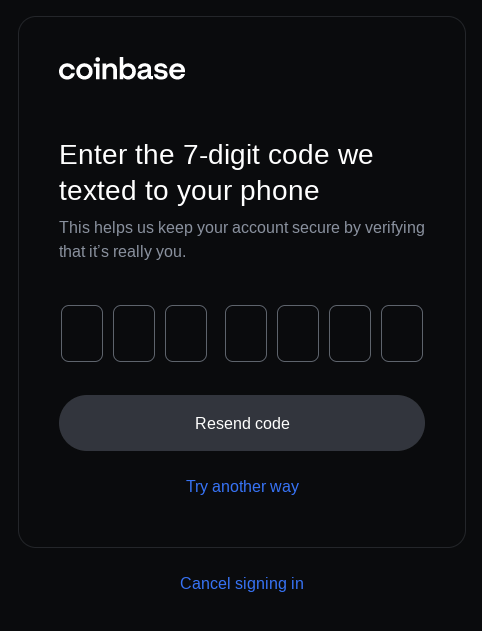
The interest of the live communication is obviously to be able to retrieve the second authentication factor (2FA) of the victim, this second factor (TOTP – Time based One Time Password) can be generated from an Authenticator app (Google Authenticator, Aegis, …) or be sent by SMS, either way the corresponding page can be presented to the victim by action from the admin panel:
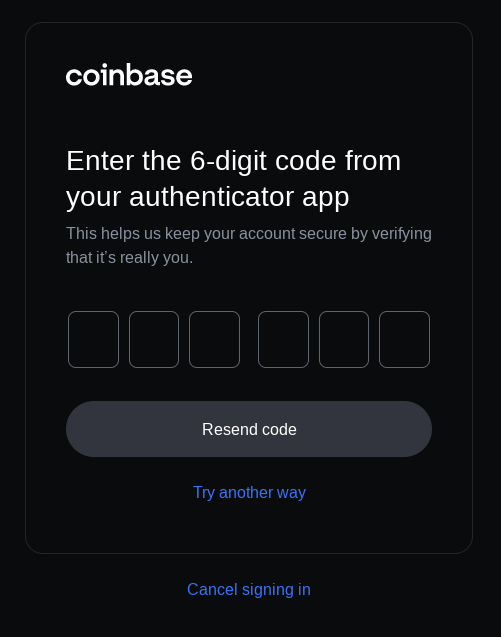
The information is then received, in real time, by the scammer through the admin panel interface:
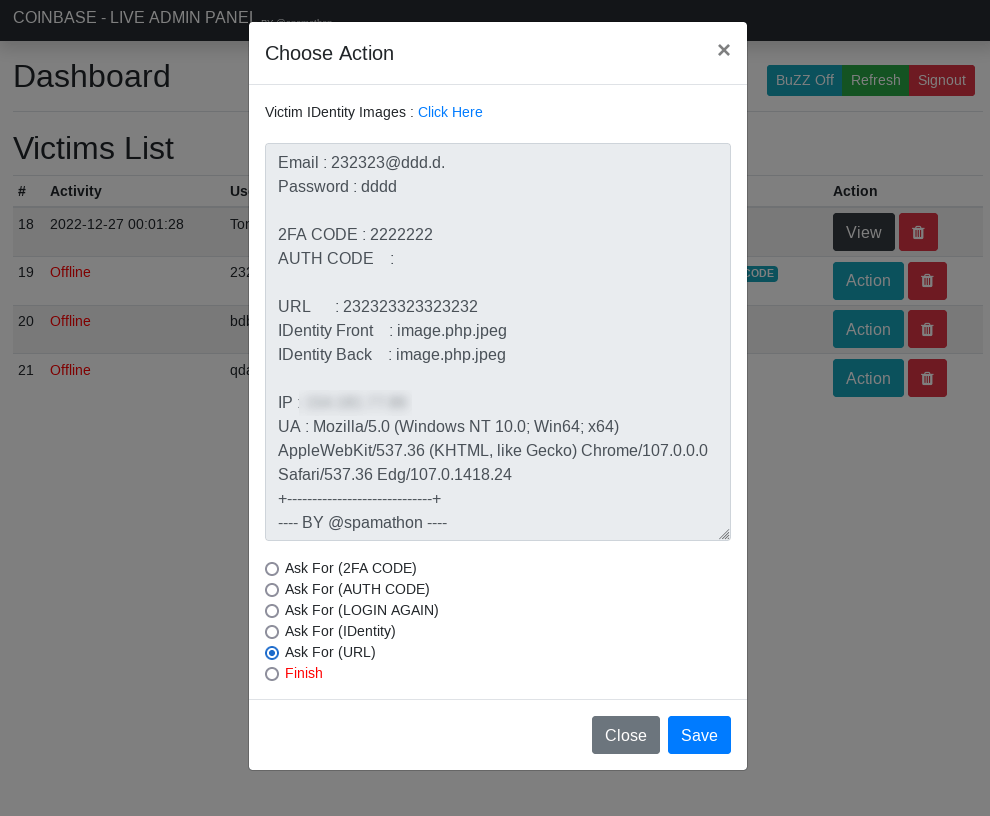
The scammer can then use the stolen credentials on the real authentication portal.
TIPS
To prevent the interception of your second factor sent by SMS (see SIM swapping) or intercepted by this kind of phishing kit, we advise you to use FIDO2 type hardware tokens, which remain, for the moment, the most adequate material to improve your authentication.
IOC
URL where we found this kit: hxxp://cbase-userhelp[.]com/Coinbase/
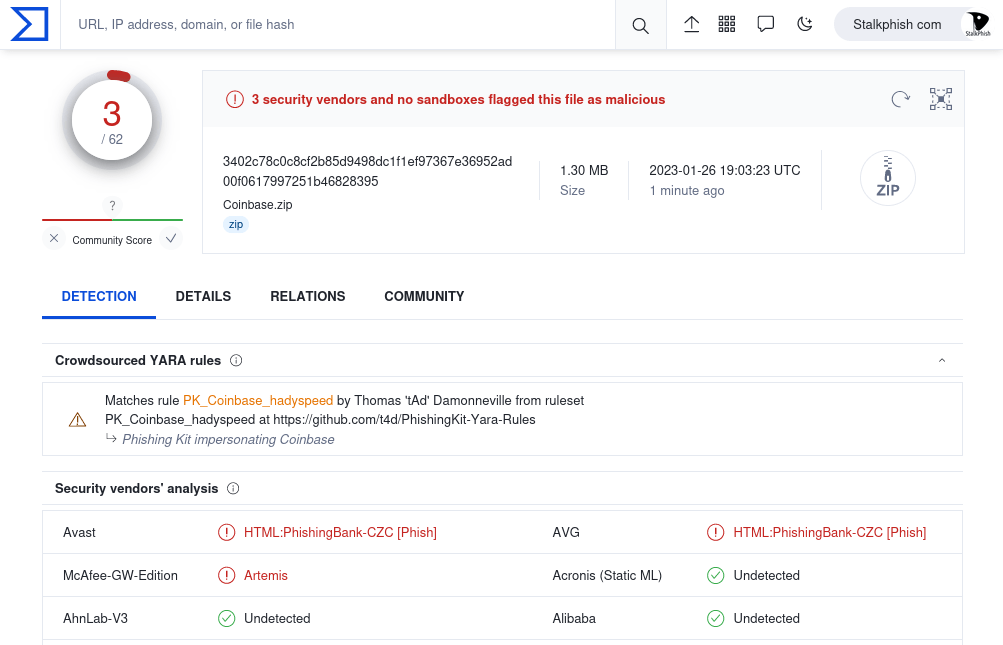
SHA256 of the zip file: 3402c78c0c8cf2b85d9498dc1f1ef97367e36952ad00f0617997251b46828395
Phishing Kit Yara Rule: PK_Coinbase_stillalive
VirusTotal analysis: https://www.virustotal.com/gui/file/3402c78c0c8cf2b85d9498dc1f1ef97367e36952ad00f0617997251b46828395
The VirusTotal analysis give the ZIP file a 2/64 score, but you can see the result of the PhishingKit Yara Rule which allows for a better contextualization of the threat:
About Stalkphish
We propose free, open source and downloadable tools, mainly focused on anti-phishing and brand identity theft (StalkPhish OSS, PhishingKit-Yara-Rules, PhishingKitHunter), check our dedicated page.
We provide enriched data related to these massive phishing campaigns, through our StalkPhish.io REST API, dedicated to digital detection and investigation of actors and their infrastructures.
Also, we regularly share knowledge and analysis of phishing kits on our StalkPhish.com (this) blog.
You can contact us for more information via our contact page.

Discover more from StalkPhish - phishing, scam and brand impersonation detection
Subscribe to get the latest posts sent to your email.

